Evaluation of Privacy-Utility Trade-off in an Adaptive Differential Privacy-Infused Secure Aggregation (ADPSA) Model for Federated Learning in IoT Environments
DOI:
https://doi.org/10.70882/josrar.2026.v3i2.176Keywords:
Differential Privacy, Federated Learning, Gradient Inversion, IoT Evaluation, Membership Inference, Privacy-Utility Trade-offAbstract
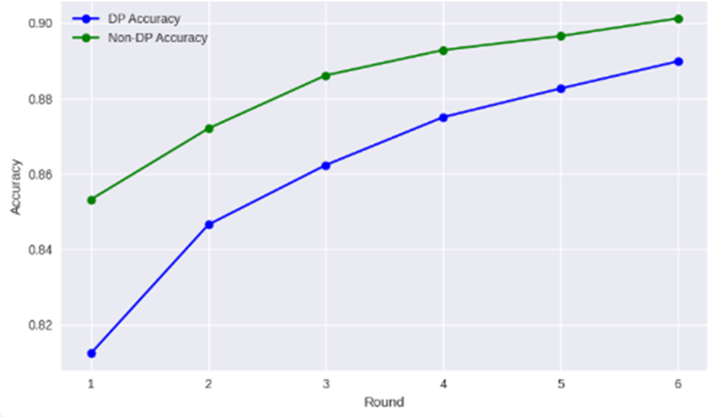
A key challenge in privacy-preserving Federated Learning (FL) is the trade-off between achieving strong privacy guarantees and maintaining high model utility. While Differential Privacy (DP) offers a formal solution, static implementations often result in excessive noise, harming accuracy. This paper presents the comprehensive evaluation of the proposed Adaptive Differential Privacy-Infused Secure Aggregation (ADPSA) model, focusing on its ability to balance privacy and utility in IoT environments. The evaluation was conducted using the N-BaIoT dataset across 100 clients for 100 communication rounds. The model was assessed against four key metrics: final privacy budget (ε), resistance to gradient inversion (measured via PSNR and SSIM), membership inference risk (attack accuracy), and final model accuracy. The ADPSA model achieved a strong final privacy budget (ε = 4.17), excellent resistance to gradient inversion (PSNR = 9.4 dB, SSIM = 0.12), and near-optimal protection against membership inference (attack accuracy = 50.9%). It maintained a high final accuracy of 90.6%, with a performance degradation of just 1.98% compared to the non-DP baseline. The results demonstrate that the adaptive privacy mechanism successfully optimizes the privacy-utility trade-off, providing strong protection with minimal impact on model performance. These characteristics make ADPSA particularly suitable for resource-constrained IoT deployments where both privacy sensitivity and computational efficiency are critical.
References
Chen, T., & Li, X. (2026). Toward trustworthy federated learning in resource-constrained IoT: A survey. ACM Computing Surveys, 58(2), Article 32. https://doi.org/10.1145/3708498
Cheng, Y., Li, W., Qin, S., & Tu, T. (2025). Differential privacy federated learning based on adaptive adjustment. Computers, Materials & Continua, 83(1), 1287–1305. https://doi.org/10.32604/cmc.2025.059063
Dritsas, E., & Trigka, M. (2025). Federated learning for IoT: A survey. Journal of Sensor and Actuator Networks, 14(1), 14. https://doi.org/10.3390/jsan14010014
Dwork, C. (2008). Differential privacy: A survey of results. In M. Agrawal, D. Du, Z. Duan, & A. Li (Eds.), Theory and applications of models of computation (TAMC 2008), Lecture Notes in Computer Science, vol. 4978 (pp. 1–19). Springer. https://doi.org/10.1007/978-3-540-79228-4_1
Kumar, A., & Das, S. (2023). Edge intelligence: A survey on federated learning in IoT environments. IEEE Internet of Things Journal, 10(4), 2823–2841. https://doi.org/10.1109/JIOT.2022.3220723
Li, T., Sahu, A. K., Talwalkar, A., & Smith, V. (2020). Federated learning: Challenges, methods, and future directions. IEEE Signal Processing Magazine, 37(3), 50–60. https://doi.org/10.1109/MSP.2020.2975749
Lu, G., Jiang, H., & Zhang, Y. (2023). DEFEAT: A decentralized federated learning against gradient attacks. High-Confidence Computing, 3(3), 100084. https://doi.org/10.1016/j.hcc.2023.100084
Luzón, M. V., García-Gil, D., Aguilera-Martos, I., & Herrera, F. (2024). A tutorial on federated learning from theory to practice: Foundations, software models, exemplary use cases, and selected trends. IEEE/CAA Journal of Automatica Sinica, 11(4), 824–850. https://doi.org/10.1109/JAS.2024.124215
Mohammadi, S., Balador, A., Sinaei, S., & Flammini, F. (2024). Balancing privacy and performance in federated learning: A systematic literature review. Journal of Parallel and Distributed Computing, 186, 104815. https://doi.org/10.1016/j.jpdc.2023.104815
Near, J., Darais, D., & Durkee, M. (n.d.). Privacy attacks in federated learning. National Institute of Standards and Technology. https://www.nist.gov/blogs/cybersecurity-insights/privacy-attacks-federated-learning
Niu, J., Chen, Z., Li, X., & Shen, J. (2024). A survey on membership inference attacks and defenses in machine learning. Journal of Information Intelligence, 2(3), 100009. https://doi.org/10.1016/j.jiixd.2024.100009
Ponomareva, N., Hazimeh, H., Kurakin, A., Xu, Z., Denison, C., McMahan, H. B., Vassilvitskii, S., Chien, S., & Ghazi, B. (2023). How to DP-fy ML: A practical guide to machine learning with differential privacy. Journal of Artificial Intelligence Research, 77, 1113–1201. https://doi.org/10.1613/jair.1.14649
Rehman, M. H. ur., Abdelmoniem, A. M., & Salah, K. (2024). Federated learning for privacy-preserving IoT: A comprehensive review. IEEE Communications Surveys & Tutorials, 26(1), 512–557. https://doi.org/10.1109/COMST.2023.3308059
Thakur, A., & Malekian, R. (2019). Fog computing for detecting vehicular congestion, an Internet of Vehicles based approach: A review. IEEE Intelligent Transportation Systems Magazine, 11(2), 8–16. https://doi.org/10.1109/MITS.2019.2903551
Wang, J., Charles, Z., Xu, Z., Joshi, G., McMahan, H. B., Al-Shedivat, M., Andrew, G., Avestimehr, S., Diao, E., Han, Y., Nock, R., Pathak, D., Richtárik, P., Sahu, A. K., Sanjabi, M., Sra, S., Subramonian, A., Suresh, A. T., Vogels, T., … Smith, V. (2021). A field guide to federated optimization [Preprint]. arXiv. https://doi.org/10.48550/arXiv.2107.06917
Zhang, L., Luo, Y., & Wang, W. (2025). Decentralized intelligence: Federated learning for next-generation IoT systems. IEEE Transactions on Network Science and Engineering, 12(3), 1845–1860. https://doi.org/10.1109/TNSE.2024.3371832
Zheng, Q., Chen, S., Long, Q., & Su, W. (2021). Federated f-differential privacy. In A. Banerjee & K. Fukumizu (Eds.), Proceedings of the 24th International Conference on Artificial Intelligence and Statistics (AISTATS), Proceedings of Machine Learning Research, vol. 130 (pp. 2251–2259). PMLR. http://proceedings.mlr.press/v130/zheng21a.html
Downloads
Published
Issue
Section
License
Copyright (c) 2026 Adewale Adebayo, Hannah Akinwumi, Micheal Agbaje, Obinna Uche, Opeyemi Shokunbi, Damilare Akinwunmi (Author)

This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.
- Attribution — You must give appropriate credit, provide a link to the license, and indicate if changes were made. You may do so in any reasonable manner, but not in any way that suggests the licensor endorses you or your use.
- NonCommercial — You may not use the material for commercial purposes.
- No additional restrictions — You may not apply legal terms or technological measures that legally restrict others from doing anything the license permits.